如果在centos下已编译安装过libgcrypt,先去到源码包make uninstall,下面使用的软件对版本要求比较严格,不是安装出错就是安装后不能使用。用到的安装包已经上传到百度网盘http://pan.baidu.com/s/1i3suZOD
1、安装 libgpg-error-1.9
1 | $ tar -zxvf libgpg-error-1.9.tar.gz |
2、安装libgcrypt-1.4.3
1 | $ tar -zxvf libgcrypt-1.4.3.tar.gz |
3、安装radiusplugin_v2.1,并将编译生成的radiusplugin.so、radiusplugin.cnf 拷贝到openvpn安装目录
1 | $ tar -zxvf radiusplugin_v2.1.tar.gz |
4、配置radiusplugin.cnf 需要注意的配置项OpenVPNConfig和server的sharedsecret
1 | $ cd /usr/local/openvpn/ |
5、OpenVPN服务端配置server.conf 需要注意的配置项tls-auth、client-config-dir、plugin
1 | $ grep -Ev "^#|^$" etc/server.conf |
其中引用的ta.key文件用来防止遭到DDoS攻击,使用openvpn命令生成。
1 | $ ./openvpn --genkey --secret ta.key |
6、OpenVPN客户端配置 将服务端的文件ta.key、ca.crt拷贝一份到客户端的C:\Program Files\OpenVPN\config文件夹下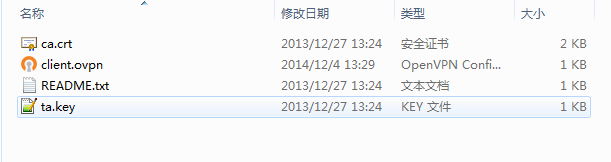
其中的配置文件client.ovpn如下:
1 | client |
重启OpenVPN 服务端后客户端就可以用“用户名/密码”的形式登录VPN了,如果要添加新的用户只需要在radius数据库的radcheck表插入新的记录即可,很是方便快捷。